During the past years, I have seen a lot of questions about setting up users who are not part of the Azure AD tenant linked to a Dynamics 365 Finance and Operations environment. Usually, there is a simple reply by stating that the Provider field on the User details should be altered to indicate where to authenticate the user. This reply does not cover the licensing requirements, components that require an app registration in Azure AD, and users not part of an Azure AD, but having e.g. a Microsoft Account. With this post, I will provide the full details to correctly enable external users.
Add users from external Azure AD
I will start with this blog with the easiest scenario: external users having an organizational account from another Azure AD tenant. When users will be added from another Azure Active Directory, the authentication should be performed by the Azure AD of the external user. Your own Azure AD would not know if the user details are valid and if the user is still an active user. For that reason, when adding the external user, you should alter the Provider field which will then know in what Azure AD the user should be verified and authenticated. The Provider field defaults with the value https://sts.windows.net/. To be able to authenticate the user in another tenant, this field needs to be changed where the domain of the user will be added at the end of the default value.
As an example, I have a Dynamics 365 F&O environment running on the tenant Dynamicspedia.com. Now I want to add a user with the email andre@axploring.onmicrosoft.com. In this case, the Provider field will be altered to have the next value: https://sts.windows.net/axploring.onmicrosoft.com. Without the correct value in the Provider field, the user will get an authentication error. Note that this procedure is not the full, correct procedure. I will elaborate in this blog on what is missing.

App registrations on Azure Active Directory
In this example, I have added the system administrator role to this user. A normal use case would be that an external consultant would set up workflow configurations or use the Open in Excel functionality. You may expect the next errors when external users try to access these functionalities.


What is causing this error and how can you solve this?
Both these examples are separate client applications, that need to be authenticated via your Azure Active Directory. For security purposes, this is not open to any tenant, so like the error mentions, you need to add the user as an external user to your tenant. Follow the next procedure in Azure Active Directory to invite external users.
- Open the Azure portal.
- Go to Azure Active Directory
- Open Manage > Users.
- Click New user > Invite external user.
- Complete the details of the external user. (There is a scrollbar at the right side which brings you to other fields below)

- Click Invite.
Users can also be created and maintained on the Microsoft 365 admin center. However, when you want to create a guest user, you will be directed to the Azure portal.
Now when the user will log in to one of the above-mentioned client applications, the authentication will be successful, but there is a confirmation required to link the user and allow for some permissions.

After accepting the permissions, the user should have access to either the workflow editor or the office add-in. I used the word ‘should’ as the workflow editor gives in some cases an error that I did not solve yet. The error I get is:
Fault was thrown bt the service for request 4d62ffa3-8170-4bf2-89b5-ffff06e2dc2f.
Exception details:
Type: System.NullReferenceException
Message: Object reference not set to an instance of an object.
The Office add-in is working like a charm using an external user. If you encounter the same issue, I would suggest logging a ticket for Microsoft Support.
When the user is added as a guest user in your Azure AD, the user will also be visible when you want to import users in Microsoft Dynamics 365 F&O from your Azure AD.
License requirements
The Microsoft Dynamics 365 licensing guide distinguishes between two types of external users. This paragraph is about the external users that are considered as internal users.
Licensing requirements for external users
External user access does not extend to your employees, onsite or independent contractors, vendors, agents, or those of your affiliates who are providing business processes on behalf of you or your affiliate. Those users are considered internal users.
These external users having access to Dynamics 365 Finance and Operations also require a valid license. To fully meet the Microsoft license requirement, the external user should be invited as a guest to the Azure AD tenant and a proper license needs to be assigned. You can read about this in the Microsoft documentation: Create new users – Finance & Operations | Dynamics 365 | Microsoft Learn. Assigning product licenses is also done in the Azure portal as the Microsoft 365 admin center is not having the option to do this. However there is no direct enforcement today, it would be a best practice to allocate the licenses just like Office 365 or Dynamic 365 Customer Engagement apps. When you want to use the Azure AD group integration in Dynamics 365 F&O, users can be automatically created in F&O, but this would require to have the license assigned already today. Personally, I thnk a next step from Microsoft could be a check for an assigned license when users will log in.
There is more…
You can also invite external users without an Azure AD account and provide access to Dynamics 365 Finance and Operations. Johan Persson wrote a blog about this option before: Adding users WITHOUT an Azure AD Accounts to Dynamics 365 for Finance and Operations – JohanPersson.nu. Where Johan mentioned Microsoft accounts, I wanted to give it a try with a Gmail account. This is also a scenario that is working. You can follow the next steps:
- Create a new guest user with a Gmail email address.

- Ensure you assign a product license to the user in Azure AD (see above).
- Import the user in Dynamics 365 Finance and Operations

- Assign the required security roles.
- Log in with the Gmail email address.

- You will be prompted to enter a code which is sent to the Gmail email address.

- Open your Gmail inbox to retrieve the verification code.

- The first time, you will be prompted to accept the requested permissions.
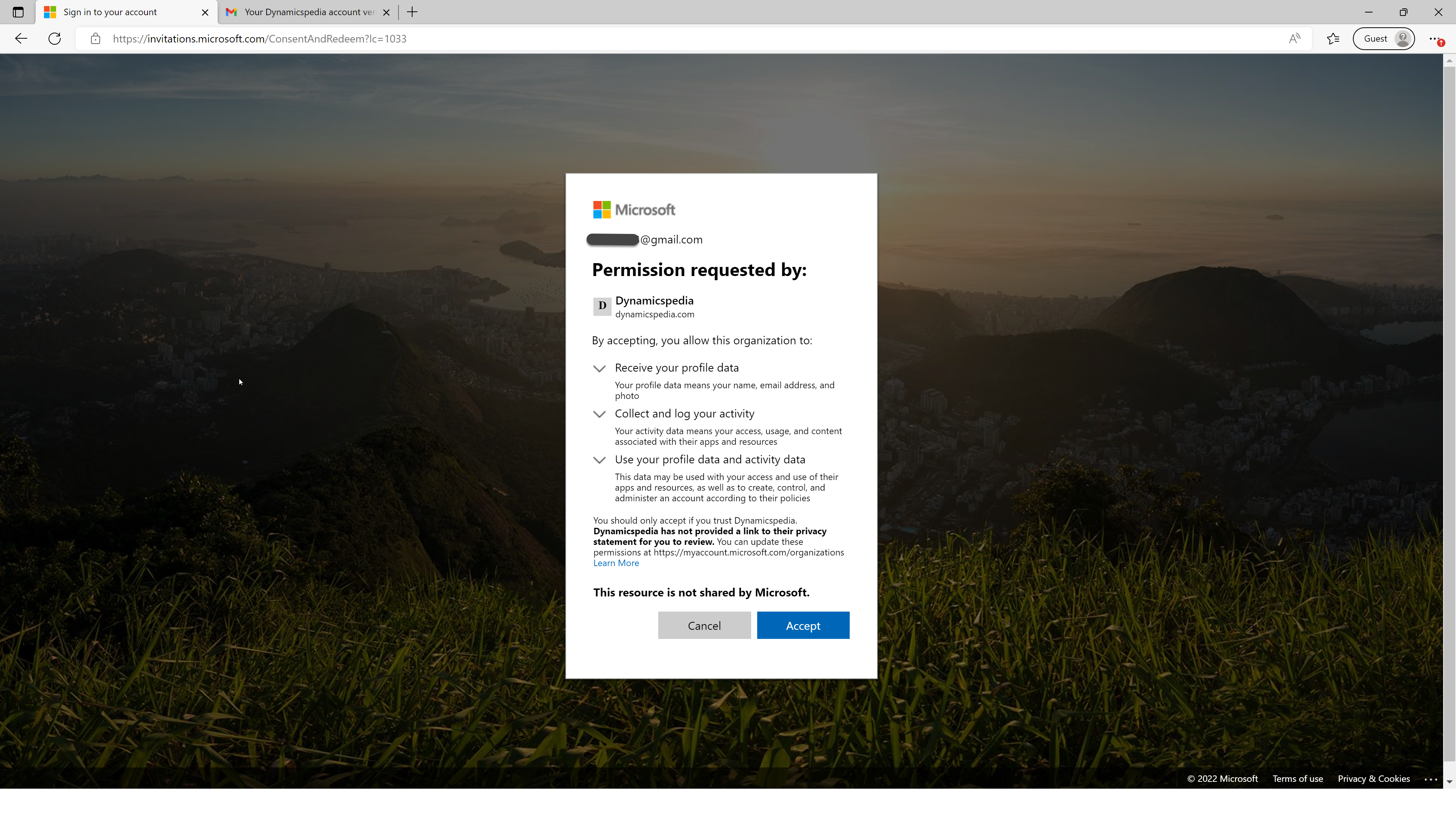
When you accepted the permissions, you will be authenticated using the Gmail email address and can access all parts of the application as per allocated security roles.
I do hope you liked this post and will add value for you in your daily work as a professional. If you have related questions or feedback, don’t hesitate to use the Comment feature below.
That’s all for now. Till next time!
s

 Image by Thomas Breher from Pixabay
Image by Thomas Breher from Pixabay 

 Original image by Ben Kerckx from Pixabay
Original image by Ben Kerckx from Pixabay  Image by DarkWorkX from Pixabay
Image by DarkWorkX from Pixabay  Image by Gerd Altmann on Pixabay
Image by Gerd Altmann on Pixabay  Image by Pexels from Pixabay
Image by Pexels from Pixabay  Image by jhenning from Pixabay.
Image by jhenning from Pixabay.
thanks for sharing. it worth nothing that AD tenant properties might have enforcement to always have AD account before you can login to FNO instance for example. the scenario mentioned above allows Direct assignment in FNO.
Thank for this André. Clearly explained.
In the last “there is more” does this external user also have license requirements?
Hi Chris,
This blog has a section about the type of external users. It highlights a section in the Dynamics 365 licensing guide where Microsoft makes a difference between different types of external users. If an external user with e.g. a Gmail account will perform tasks like creating customers and entering sales orders like an internal employee, in that case, this external user should have an appropriate license.
If you invite external users to complete certain tasks related to an HR job recruitment process, in that case, the external users should not have a license assigned.
At least, these thoughts are based on my understanding of the Dynamics 365 Licensing guide.
Hi Chris,
We planned to allow our partner under b2b guest authentication ()partner domain is federated in Gsuite- federated allowing as guest and user receiving invitation and . it hitting to ERP page and facing attached issue.
Your not authorized to login with your current credentials. you will be redirected to the login page in a few seconds.
If you invite a user from an external Azure AD, I understand they will need to be licensed, but how would that effect things like emailing? Say they want to send an email from Business Central, would the email come from their own email address and from their own tenant or would it not work at all? What would happen there?
Hi Sam,
You mentioned Business Central in your comment. My post is written for Finance and Operations. I’m not able to provide the correct reply for Dynamics 365 BC. I would suggest asking your question on the Dynamics Community: Dynamics Community Forum – Business Central